Although hacking expanded and enjoyed glorification during the 80s, a divide was forming within the hacking community by the end of the decade. The hacker principle of “freedom of technology” was changing, and a younger generation interested in individual gain emerged leading to an increase in the number of hackers that were no longer satisfied with benign exploration of systems merely to learn how they worked.
This obscure side fragmented even further as several independent groups formed “electronic gangs,” driven to tap into the sensitive information housed within large institutions, like government and educational research centers. Similarly to what happens with conventional street gangs, it did not take long for these groups to begin fighting each other, and the early 1990s saw an escalation of infighting that jammed phone lines and networks, and ultimately led to the demise and criminal prosecution of several groups. On top of this, the end of the cold war is a very significant factor as it allows the Internet to spread freely across the former URSS, with great impact on both sides of the now rusty Iron Curtain.
Historical Landmarks:
1990
The
Great Hacker War begins with Legion of Doom and Masters of Deception engaging in almost two years of online warfare –jamming phone lines, monitoring calls, trespassing in each other's private computers.
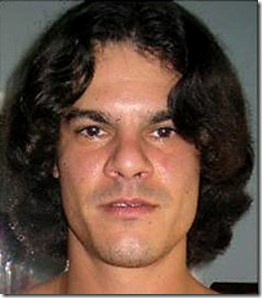
In response to the AT&T telephone system crash that left 60,000 customers without a phone line for nine hours on January 15, federal authorities burst into Mark Abene's (
Phiber Optik) bedroom, guns drawn, and confiscate his computer equipment. Abene and other MOD members have their homes searched and property seized by the U.S. Secret Service largely based on government suspicions of having caused AT&T Corporation's network crash. Some weeks later, AT&T themselves admit that the crash was the result of a flawed software update to the switching systems on their long distance network, thus, human error on their part.

A role-playing game company called
Steve Jackson Games in Austin, Texas is raided. The Secret Service seizes computers and disks at the company‘s offices and also at the home of one of their employees, Loyd Blankenship (The Mentor) a former member of the Legion of Doom. Blankenship is writing a role-playing game called GURPS Cyberpunk, which the agents interpret as a handbook for computer crime.

After two years of investigation, 150 FBI agents, aided by state and local authorities, launch
Operation Sundevil raiding presumed criminal hacker organizations allegedly involved in credit card abuse and theft of telephone services. They seize 42 computers and 23,000 disks from locations in 14 cities. The result is a breakdown in the hacking community, with members informing on each other in exchange for immunity as the targets were mainly sites running discussion boards, some of which were classified as hacker boards.
The legal battles arising in the aftermath of Operation Sundevil, the Steve Jackson Games raid and the trial of Knight Lightning, prompt the formation of the
Electronic Frontier Foundation. John Perry Barlow and Mitch Kapor form this organization when they felt that there was a need for increased protection for Internet civil liberties.

The Internet has more than 300,000 hosts and while the T3 lines are being constructed, the Department of Defense disbands the ARPANET and most university computers that were connected to it are moved to networks connected to the National Science Foundation Network (
NSFNET). The original 56Kbs lines of ARPANET are taken out of service being replaced by the NSFNET backbone.

Australian federal police tracking
Realm members Phoenix, Electron and Nom are the first in the world to use a remote data intercept to gain evidence for a computer crime prosecution.
The
Computer Misuse Act is passed in the United Kingdom, criminalizing any unauthorized access to computer systems.
Each week, the Los Angeles KIIS-FM radio station ran the “Win a Porsche by Friday” contest, with a $50,000 Porsche given to the 102nd caller after a particular sequence of songs announced earlier in the day was played. Kevin
Poulsen
(Dark Dante) and his associates, stationed at their computers, seized control of the station’s 25 telephone lines, blocking out all calls but their own. Then he dialed the 102nd call — and later collected his Porsche 944.
1991
Although Abene is ultimately acquitted in the AT&T scandal, in February he is arrested and charged with computer tampering and computer trespass in the first degree. Being a minor, he pleads "not guilty" and ultimately accepts a plea agreement to a lesser misdemeanor charge, and is sentenced to 35 hours of community service.
Philip Zimmerman releases "
Pretty Good Privacy" (PGP), a free, powerful data-encryption tool. The U.S. government begins a three-year criminal investigation on Zimmerman, alleging he broke U.S. encryption laws after his program spread rapidly around the globe.

The first browsable directory of files on the Internet,
Gopher, is created providing a text based, menu-driven interface to access internet resources.
Wide Area Information Servers (
WAIS) is created providing a mechanism for indexing and accessing information on the Internet.
The federal ban barring business from the Internet is lifted and the Commercial Internet eXchange (
CIX) Association, Inc. formed after NSF lifts restrictions on the commercial use of the Net.
Linus Torvalds publicly releases
Linux version 0.01
 World-Wide Web
World-Wide Web (WWW) released by CERN. Originally developed by Tim Berners-Lee to provide a distributed hypermedia system it allows easy access to any form of information anywhere in the world.
 Justin Petersen
Justin Petersen, arrested three months earlier for hacking, is released from prison to help the FBI track hacker Kevin Mitnick .
Michelangelo virus media panic begins.
Kevin Poulsen is arrested on charges of fraud and money laundering, after being featured on an episode of "Unsolved Mysteries".
By the end of the year
Phiber Optik has appeared in Harper‘s Bazar, Esquire, The New York Times, in countless public debates and conventions and even on a television show hosted by Geraldo Rivera. He and four other members of the Masters of Deception are also arrested in December as a result of a major nationwide investigation by a joint FBI/Secret Service task force.
1992
A group of computer enthusiasts arranges to store their spare equipment in some rented space in Boston. They collaborate on analysis of vulnerabilities, especially on Microsoft products, and gain a reputation for contributing serious research to the field and for appearing at security conferences. It's the birth of
L0pht Heavy Industries. 
Bruce Sterling publishes
The Hacker Crackdown, in which he documents a mounting legal resistance to hackers, provides an in-depth look at several actual hacks, and discusses the civil liberties side of hacking. The book gives the public yet another glimpse into the underworld of hacking, cracking, and phreaking. The combination of these events publicizes the dark side of hacking and raised the public’s awareness to its consequences.

Bulgarian virus writer
Dark Avenger writes 1260, the first polymorphic virus. It is the first known use of a polymorphic engine to mutate the virus code while keeping the original algorithm intact. The idea behind the use of this polymorphic code, is to circumvent the type of pattern recognition used by Anti-virus software.
Five
MOD members are indicted by federal court an 11-count charge. The indictment relies heavily on evidence collected by court-approved wire tapping of telephone conversations between MOD members.
The number of
Internet hosts exceeds 1 Million.
The term "
Surfing the Internet" is coined by Jean Armour Polly.
1993
Wired magazine is released.

Court rules in favor of
Steven Jackson Games and the Secret Service is ordered to pay damages.
The First
DefCon hacker conference is held in Vegas with the single purpose to say good-bye to BBSs (now replaced by the Web), but the gathering is so popular it became an annual event.

The
Mosaic web browser is released, popularizing the World Wide Web. Developed at the National Center for Supercomputing Applications (NCSA), it provides a multimedia graphical interface that allows users to more easily navigate the web by converting text commands to images.

All five MOD member plead guilty and are sentenced to either probation or prison.
Phiber Optik serves one year in a federal jail.
1994
Usenet becomes a popular target for spam messages. The
first mass spam is sent by Clarence Thomas, a system administrator Andrews University. His message: Global Alert for All: Jesus is Coming Soon.
Mosaic is renamed
Netscape Navigator and the company takes the 'Netscape' name.

Brian Pinkerton creates
WebCrawler, the first Web search engine. It is a software robot that collects the full text of web pages and stores them in a database that can be searched using keywords. As other robots were developed to search the Web, they became known as "crawlers" or "spiders".

In addition to WebCrawler, EINst Galaxy, Lycos and Yahoo! search engines were created.
30-year-old Russian
Vladimir Levin leads a group of hackers who break into Citibank's systems and steal 10 million dollars. Using his work laptop after hours, he transfers the funds to accounts in Finland and Israel. Levin stands trial in the United States and is sentenced to three years in prison.
AOHell is released as a freeware application that allows unskilled script kiddies to wreak havoc on America Online. For days, hundreds of thousands of AOL users find their mailboxes flooded with multi-megabyte email bombs and their chat rooms disrupted with spam messages.
16-year-old student, nicknamed “
Data Stream”, arrested by UK police for penetrating computers at the Korean Atomic Research Institute, NASA and several US govt. agencies.
Five members of the Aum Shinri Kyo cult's Ministry of Intelligence break into
Mitsubishi Heavy Industry's mainframe and steal a significant amount of sensitive data.
Prof. James Der Derian coins term "
cyber deterrence" in Wired Magazine.
Kevin Poulsen pleads guilty in U.S. District Court in Los Angeles to seven counts of mail, wire and computer fraud, money laundering and obstruction of justice in connection with the KIIS-FM incident and others.
A hacker steals
Tsutomu Shimomura's personal files and distributes them over an online community for expert computer programmers. The culprit is Kevin Mitnick.
The Intervasion of the UK orchestrated by a group called the Zippies on Guy Fawkes Day, is the first public use of
DDoS as a form of protest.
A husband and wife team of lawyers, Laurence Canter and Martha Siegel, use bulk Usenet posting to advertise immigration law services creating the
first major commercial spam incident when they cross-post their Green Card Assistance Services to 6,000 newsgroups at once. The enraged Usenet users reply with insulting email messages (flames) and mail-bombs (a large email that takes up a huge amount of space on the receiver's server that clogs the system and can cause it to crash). Defiant in the face of widespread condemnation, the attorneys claimed their detractors were hypocrites or zealots and write a controversial book entitled
How to Make a Fortune on the Information Superhighway: Everyone's Guerrilla Guide to Marketing on the Internet and Other Online Services." In this book, they support spamming as a viable marketing tool and they claim everyone has a right to advertise on all the newsgroups in any way as they saw fit. This sets a precedence that most spammers still abide by: If you don't like it, delete it, we're just exercising our right to free speech.
1995
Alta Vista, Excite, and InfoSEEK
search engines are created.
Microsoft releases
Windows 95. Anti-virus companies worry that the operating system will be resistant to viruses.
 Macro viruses
Macro viruses appear and are able to corrupt the new Windows operating system.
Microsoft releases
Internet Explorer as part of the Windows 95 Plus! Pack.

Using a trace-dialing technique and locating telephone loop signals,
Tsutomu Shimomura, from the San Diego Supercomputer Center tracks down Kevin Mitnick.

In a highly publicized case,
Kevin Mitnick, probably the world’s most prolific and best-known hacker, is arrested (again), this time in Raleigh, N.C., He is charged with stealing at least $1 million worth of sensitive project data from computer systems.
Mitnick is the very first person to be convicted of gaining access to an interstate computer network for criminal purposes and is also the first cracker to have his face appear on an FBI "Most Wanted" poster.

Mitnick is charged of snagging thousands of credit card numbers from online databases, breaking into the California motor vehicles database, and remotely controlling New York and California's telephone switching hubs on various occasions. Mitnick is a master of what hackers refer to as social engineering, gathering information simply by asking people for it. Many times the passwords he used to enter computer networks were provided by the systems administrators of those networks, who had been convinced that Mitnick had good reasons for needing the passwords. He will remain in jail for 4 years without trial.
The "Netstrike", a strike action directed against French government computers is one of the earliest documented
hacktivist events.
Spamware, or spamming software is created. In August, a list of two million e-mail messages is offered for sale.
Kevin Poulsen is sentenced to 51 months in prison and over $56,000 in restitution to radio stations he scammed.
1996
Cult of the Dead Cow member Omega coins the term "
hacktivism."
Hackers deface the Web sites of the United States Department of Justice, the
CIA, and the U.S. Air Force.
Canadian hacker group,
Brotherhood, angry at hackers being falsely accused of electronically stalking a Canadian family, breaks into the Canadian Broadcasting Corporation web site and leave message: "The media are liars." Family's own 15-year-old son eventually is identified as stalking culprit.
The U.S. General Accounting Office reports that hackers attempted to break into
Defense Department computer files some 250,000 times in 1995 alone. About 65 percent of the attempts were successful, according to the report.
John Deutsh, CIA director, testifies foreign organized crime groups behind hacker attacks against the US private sector.
US Communications Decency Act (CDA) passed – makes it illegal to transmit indecent/obscene material over Internet.
South Korean media reports that
North Korean government officials are engaging in efforts to obtain foreign proprietary technology through indirect methods.
Bell Research Labs in the US announce they have found a way to counterfeit the electronic money on smart cards.
A computer hacker allegedly associated with the
White Supremacist movement temporarily disabled a Massachusetts ISP and damaged part of the ISP's record keeping system. The ISP had attempted to stop the hacker from sending out worldwide racist messages under the ISP's name. The hacker signed off with the threat, "you have yet to see true
electronic terrorism. This is a promise."
1997
US Supreme court rules Communications Decency Act (
CDA) unconstitutional.
America On-line (AOL), one of the largest Internet service providers in the US, cuts direct access for its users in Russia due to the high level of fraud.
The german
Chaos Computer Club claims it was able to penetrate Microsoft's Internet software and the financial management program
Quicken, and transfer money between accounts without either the account holder or bank realizing the transaction was unauthorized.
FBI’s
National Computer Crimes Squad reports 85% of companies have been hacked, and most never know it.
A hacker disables the computer system of the airport traffic control tower at
Worcester Airport, Massachusetts. No accidents are caused, but regular service is affected.
A hacker from Sweden jams the
911 emergency telephone systems in the west-central Florida. This indicates that an attack could be launched from anywhere in the world.
Electronic Disturbance Theater (EDT) starts conducting Web sit-ins against various sites in support of the Mexican Zapatistas. At a designated time, thousands of protestors point their browsers to a target site using software that floods the target with rapid and repeated download requests. Animal rights groups have also used EDT's software against organizations said to abuse animals.
A 15-year-old Croatian youth penetrates computers at a U.S. Air Force base in
Guam.
The
Eligible Receiver 97 exercise tests the American government's readiness against cyberattacks. The NSA Red Team used hacker techniques and software that was freely available on the Internet at that time. The Red Team was able to crack networks and do things such as deny services; change and manipulate emails to make them appear to come from a legitimate source; disrupt communications between the National Command Authority, intelligence agencies, and military commands. Common vulnerabilities were exploited which allowed the Red Team to gain root access to over 36 government networks which allowed them to change/add user accounts and reformat server hard drives.
First high-profile attacks on Microsoft's
Windows NT operating system.
Sanford Wallace, “The Spam King”, starts his of spamming career creating a spamming company called Cyber Promotions to send junk faxes and then moves to email and other Internet tactics.

A group calling themselves
PANTS/HAGIS Alliance hacks Yahoo! and threatens to set off a computer virus. Yahoo! notifies internet users that anyone visiting its site in recent weeks might have downloaded a logic bomb and worm planted by hackers claiming a "logic bomb" will go off on Christmas Day 1998 if Kevin Mitnick is not released from prison. It turns out to be just a hoax.
The Portuguese hacking group
UrBaN Ka0s hacks the site of the Republic of Indonesia and 25 other military and government sites as part of the hacking community campaign against the Indonesian government and the state of affairs in East Timor.
1998
Search giant
Google is founded by Larry Page and Sergey Brin in the follow-up of their research project of while studying for their Ph.Ds. at Stanford University.
Intruders infiltrate and take control of more than 500 military, government and private sector computer systems. The attacks, dubbed "
Solar Sunrise" after the well-known vulnerabilities in Sun's Solaris operating system, implant sniffer programs to pilfer sensitive data and appear to come from servers around the world. Investigators originally suspect operatives in Iraq, but later learn that a group of California teenagers was responsible for the incursions. The experience gives the US Department of Defense its first taste of what hostile adversaries with greater skills and resources would be able to do to the nation's command and control center, particularly if used in tandem with physical attacks.
CIA Director George Tenet gives speech on "information security risks" and, for the first time, a US spy chief refers publicly to the threat of "
cyberattack."
US military coordinates cyberdefense efforts under a Joint Task Force – Computer Network Defense.
Ethnic Tamil guerrillas swamp Sri Lankan embassies with over 800 e-mails a day for more than two weeks. The messages read, "We are the
Internet Black Tigers and we're doing this to disrupt your communications."Intelligence authorities claim this is the first known attack by terrorists against a country's IT infrastructure.
U.S. Attorney General
Janet Reno unveils National Infrastructure Protection Center, which is given a mission to protect the nation's telecommunications, technology and transportation systems from hackers.
The members of the elite hacker group known as
L0pht testify in front of the US congressional Government Affairs committee on "Weak Computer Security in Government". L0pht claims it can shut down nationwide access to the Internet in less than 30 minutes and therefore the group urges stronger security measures.
Hackers break into
United Nation's Children Fund Web site, threatening a "holocaust" if Kevin Mitnick is not freed.
Information Security publishes its first annual Industry Survey, finding that nearly 75% of organizations suffered a security incident in the previous year.
The
Federal Bureau of Labor Statistics is inundated for days with hundreds of thousands of fake information requests.
Hacking group Cult of the Dead Cow releases a Trojan horse program called
Back Orifice at Defcon. Once installed a Windows 9x machine the program allows for unauthorized remote access.
 Timothy Lloyd
Timothy Lloyd is indicted for planting a logic bomb on the network of Omega Engineering, causing millions in damage.
Hackers alter
The New York Times Web site, renaming it HFG (Hacking for Girlies).
During heightened tensions in the Persian Gulf, hackers break into unclassified
Pentagon computers and steal software programs allegedly for a military satellite system. They threaten to sell the software to terrorists.
U.S. officials accidentally discover a pattern of probing of computer systems at The Pentagon, NASA, United States Department of Energy, private universities, and research labs. This series of incidents form an operation later to be known as
Moonlight Maze in which hackers penetrate American computer systems systematically marauding through tens of thousands of files - including maps of military installations, troop configurations and military hardware designs.
The
Legions of the Underground (LoU) declare
cyberwar on Iraq and China with the intention of disrupting and disabling their Internet infrastructure.
1999
An international coalition of hackers (including Cult of the Dead Cow, 2600's staff, Phrack's staff, L0pht, and the Chaos Computer Club) issue a joint statement condemning the LoU's declaration of war. The LoU responds by withdrawing its declaration.
US Defense Dept. acknowledges 60-80 attacks per day.
Assassins hack into a hospital computer to change the medication of a patient so that he would be given a lethal injection. He is dead within a few hours.
Hackers in
Serbia attack NATO systems in retaliation for NATO’s military intervention in Kosovo. Computers are blasted with e-mail bombs and hit with denial-of-service attacks. In addition, many businesses, public organizations, and academic institutes have their websites defaced.
NATO accidentally bombs the Chinese embassy in Belgrade, spawning a wave of cyberattacks from China against U.S. government Web sites where Chinese hacktivists post messages such as "We won't stop attacking until the war stops!"
Electrohippies, another group of hacktivists, conducted Web sit-ins against the WTO when they meet in Seattle.
The
Electronic Civil Disobedience project, an online political performance-art group, uses the FloodNet software to attack the Pentagon calling it conceptual art and claiming it to be a protest against the U.S. support of the suppression of rebels in southern Mexico by the Mexican government.
Cult of the Dead Cow releases
Back Orifice 2000 at DEF CON.

A hacker interviewed by Hilly Rose during the Art Bell Coast-to-Coast Radio Show exposes a plot by Al-Qaida to derail
Amtrak trains. This results in all trains being forcibly stopped over Y2K as a safety measure.
Hacktivists attempt to disrupt
ECHELON (an international electronic communications surveillance network filtering any and all satellite, microwave, cellular, and fiber-optic traffic) by holding "Jam Echelon Day" (JED).
New Jersey programmer David Smith unleashes the first self-replicating worm to attack the Internet since Robert Morris' 1988 worm. Traveling via Microsoft Outlook email software,
Melissa (named after a bar dancer) brings down computer networks at some 300 corporations. The virus is attached along with emails which have the following message: “Here is that document you asked for, don’t show it to anybody else.” As soon as it is activated, it sends copies of itself to the first 50 names listed in the recipient's Outlook e-mail address book. It also infects Microsoft Word documents on the user's hard drive, and mails them out through Outlook to the same 50 recipients.

Kevin Mitnick, detained since 1995 on charges of computer fraud, signs plea agreement and is sentenced to 5 years of which over 4 years had already been spent pre-trial.
Final words:
By the late 1990s hacking comes full circle and is the subject of scholarly research and discussion. Major colleges and universities are teaching and establishing programs of study focused on cyberculture and cyber security. The hacker mystique is continuously growing and evolving since its early days as a benign activity carried out within obscure computer labs in the 1960s. Participants have played many different roles and have been popularized through many mediums. They have been everything from computer tourists and network voyeurs to dangerous
criminals and nihilist anarchists; from computer nerds to cyberpunks; from public nuisance to catalysts for technology advancement. No matter how much new legislation passes or how many new security roadblocks are devised, hacking will be practiced as long as computers and technology-driven communication systems are with us. However, this is also the end of anarchy, the death of the frontier. Hackers are no longer considered romantic antiheroes, kooky eccentrics who just wanted to learn things. A burgeoning online economy with the promise of conducting the world's business over the Net needed protection. Suddenly hackers are crooks.
Previous Chapter –
Next Chapter: A New World (2000s)